Posts tagged: database
Database Tip: Clean Up User-Agent Data
I just finished up my latest book, Wizard’s SQL Recipes for WordPress. And it’s packed with over 300 time-saving code snippets for managing and optimizing your WordPress database. For example, one of the recipes from the book shows how to delete unwanted user-agent data from the WP comments table. This is an easy optimization step that can help to free up some precious disk space.

Subscribe to Comments Plugin: Delete Data from Database
During the latest site redesign, I removed the Subscribe to Comments plugin. Wisely, the plugin does not delete any subscriber information from the database. So as a part of the site’s redesign slash clean-up, I wanted to export/save and then delete all subscriber information to decrease overall database size. After searching and not finding any specific solution or preferred technique for this process, I rolled my own. Actually it’s just a simple SQL query to get it done! :)
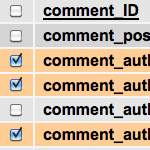
Get Comment Info from the WordPress Database
An easy way for visitors to enter their emails is by commenting on a post. We did this recently for people to sign up for a notification email. Instead of using a plugin or custom function for a one-time email list, we just went with WordPress core functionality and used post comments for people to sign up. Then the trick is retrieving the comment information from the database for the sign-up post.
Clean Up Weird Characters in Database
It’s been a crazy month, with lots of drama all over the place. Here at DigWP.com, we had an episode where the site was all screwed up and not loading or only partially loading, blank white pages, and the whole bit. During the process of keeping it together and trying to restore full functionality, numerous database imports and exports were performed under a variety of circumstance. During the rush, apparently the most recent database backup file was somehow uncompressed outside of MySQL before final import.
Several days later, that decompression/unzipping basically converted every quotation mark, em dash, en dash, ellipses and other special characters into some really ugly-looking codes.

Change Your Database Prefix to Improve Security
One of the awesome things about WordPress is that it’s a dynamic publishing system that uses a database to store your site’s information: posts, options, plugin and theme settings – all of this data is stored in your site’s database. It’s like the brain of your WordPress installation.
Unfortunately the WordPress database is also a prime target in many website attacks. Spammers and other bad guys target various database tables with automated scripts, SQL injection, and other malicious code. Needless to say it’s critical to protect your database and keep recent backups. One of the smartest ways to protect your site’s database is to change the default table prefix to something obscure and difficult to guess. Sort of like a password.

Pimp your wp-config.php
Easily, the most important file in your WordPress installation is the wp-config.php file. It serves as your site’s base configuration file, controlling key aspects of WordPress’ functionality and enabling WordPress to do mission-critical stuff like connect to the database. Without wp-config.php, WordPress simply won’t work. So whenever you install WordPress, one of the first things to do is pimp your wp-config.php with some custom WP configuration tricks.

Easy Comment Management via SQL Queries
Here are some sweet SQL code snippets for easy comment management. Sometimes it’s easier to modify comment status and delete unwanted comments on a sitewide basis. Using a program like phpMyAdmin makes it so easy to do stuff like remove spam, close/open comments on old posts, enable/disable pingbacks for specific time periods, and so on. Just remember to backup your database before running any queries (just to be on the safe side).

Media Temple WordPress Hack
It looks like Media Temple WordPress installs have been hit with a WordPress Redirect Exploit1. We got hit here at DigWP.com, but have cleaned things up and are taking steps to prevent it from happening again. This post briefly explains the hack, and provides some steps that you can take to remove the payload and get back on track.

WordPress Security Lockdown
This article is split into two parts for ez reference. First some information on the evil WordPress “Pharma Hack”, and then a recipe for protecting your site with a solid security lockdown. Choose your own adventure:

Remove/Replace Content from the WordPress Database
A useful tool to have in in your WordPress toolbelt is the ability to quickly and easily search for, find, and replace specific strings of text directly from the MySQL database. We can do this by entering SQL queries either directly or through one of those handy interface applications like phpMyAdmin, which seems like one of the most prevalent PHP applications on servers today.
Create a Custom Database Error Page in WordPress
As a dynamic blogging system, WordPress consists of PHP files (the WP core) that interact with a MySQL database to generate the web pages for your website. When everything is working properly, this dynamic interaction keeps WordPress humming along like a champ, but when your database crashes, WordPress can’t operate and will deliver the following message to your visitors:

How to Secure Your New WordPress Installation
One of the best ways to ensure strong security for your WordPress-powered site is to secure its foundations during the installation process. Of course these techniques can be implemented at any point during the life of your site, but stetting them before the game starts prevents headaches and saves time. We’ll start with the WordPress database..

Show Off Your WordPress Database Statistics
Hello WordPress peeps! Did you know that WordPress makes it super-easy to display some basic statistics about your database performance? The information may be displayed publicly on your web page, slightly hidden in your source code, or entirely private so only you can see it. There are two basic statistics that are drop-dead easy to include on your pages:
Mastering WordPress Post-Revisioning and Auto-Save Features
Not everyone loves the post-revisioning feature of WordPress. In fact, some people can’t stand it. On the one hand, it’s nice to have a library of post-draft revisions to drudge through if you should ever make a mistake. On the other hand, multiple copies of every post is a great way to bloat your database with otherwise useless information.