Posts tagged: Security
About the “Warning! WordPress Encrypts User Cookies” Error
Upgrading from older versions of WordPress is designed to go without a hitch, but depending on the setup and the two versions involved, you may encounter some hangups along the way. For example, if you are upgrading from a version of WordPress older than 3.0, eventually you may encounter the dreaded “Warning! WordPress Encrypts User Cookies” error. This quick DigWP tutorial explains what it is, why it happens, and how to fix the problem asap.
Banhammer!
Announcing my latest WordPress security plugin, Banhammer! It makes monitoring site traffic and banning unwanted guests waay too much fun. Navigate logged requests via slick Ajax UI, and enable sound effects for banning and warning bad users and bots. Check out the video on YouTube and download Banhammer from the WP Plugin Directory.
Update! Banhammer Pro now available :)

Tips to Keep WordPress Secure
With each passing day, strong security becomes more important. This article explains some ways to keep WordPress secure while improving the overall security of your WordPress-powered site. Most of the tips provided here are practice-based security steps that require no plugins or hacks. The idea here is that you don’t need to make changes to any code, or modify WordPress in any way in order to maintain strong security. These are security steps that most any WordPress user can use to help protect their site and keep WordPress safe and secure.
Clean Up “Cannot redeclare” Hack
One of my clients was hacked with the so-called Cannot redeclare hack. It seems closely related to the nefarious TimThumb hack, so if you’ve been hit by either of these hacks, you should check for the other. Apparently these hacks affect shared servers, so if you host multiple WordPress sites, chances are high that they’re all infected.

Secure uploads, upgrade and other directories with .htaccess
It sucks, but a lot of plugins require certain directories to be set at CHMOD 777 for its file permissions. Of course, you should not use any plugin that requires 777 directories, but if you absolutely must, you can help protect the folder by adding a thin slice of htaccess. This works great for any directory requiring “loose-ish” permissions (i.e., anything greater than 755), and may also be useful for other key folders as well.
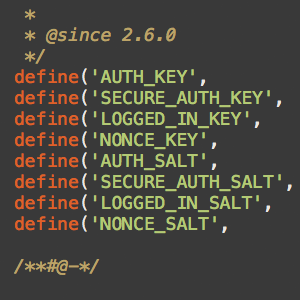
WordPress Security Keys
In our recent post on pimping the wp-config.php file, we explain that using strong Security Keys is an important part of securing your WordPress installation. In this post, we want to zoom-in on Security Keys and look at what they are, how they work, and how to use them to greatly improve the security of your site.

Pimp your wp-config.php
Easily, the most important file in your WordPress installation is the wp-config.php file. It serves as your site’s base configuration file, controlling key aspects of WordPress’ functionality and enabling WordPress to do mission-critical stuff like connect to the database. Without wp-config.php, WordPress simply won’t work. So whenever you install WordPress, one of the first things to do is pimp your wp-config.php with some custom WP configuration tricks.

Add Private Content to Posts via Shortcode
Recently, WP-Mix posted an incredibly useful technique that uses a shortcode to add private content to blog posts. This functionality makes it easy to manage leftover data, miscellaneous notes and other communication by keeping everything together with its corresponding post. Consolidating information like this helps to streamline flow and organization into the future.
WordPress Defender: 30 Ways to Secure Your Website
Looking for a good book on WordPress security? If so, we’ve got great news! John Hoff’s new security e-book WordPress Defender provides 30 practical ways to secure your website from the evil forces of spam, bad bots, and malicious hackers. The book is packed with practical, common-sense security techniques that virtually any WordPress user can use to protect their site from malicious threats.

Stop Spammers with a Custom Comment Blacklist
I usually reserve most of my blacklisting content for Perishable Press, but after posting about using WordPress’ built-in tools to stop comment spam, several DiW readers have asked about a good custom blacklist that may be used for the “Comment Moderation” and/or “Comment Blacklist” features in the WordPress “Discussion Settings” screen. Over the years, I have built up an extensive custom blacklist of terms that has proven quite effective at keeping spam and other garbage out of the comments section, even without using any anti-spam plugins such as Akismet. It’s strictly plug-n-play, and should help protect your site (and reputation) against all sorts of malicious nonsense.
Create a Custom Database Error Page in WordPress
As a dynamic blogging system, WordPress consists of PHP files (the WP core) that interact with a MySQL database to generate the web pages for your website. When everything is working properly, this dynamic interaction keeps WordPress humming along like a champ, but when your database crashes, WordPress can’t operate and will deliver the following message to your visitors:

How to Secure Your New WordPress Installation
One of the best ways to ensure strong security for your WordPress-powered site is to secure its foundations during the installation process. Of course these techniques can be implemented at any point during the life of your site, but stetting them before the game starts prevents headaches and saves time. We’ll start with the WordPress database..

Optimize WordPress Performance with wp-config.php
As you may recall, there are a ton of configuration tricks available for the WordPress wp-config.php file. So many in fact, that I think many people may have missed some of the choice definitions aimed at optimizing WordPress performance. In this post, we’ll explore the best ways to improve your site’s performance with WordPress’ wp-config.php file.

WordPress Configuration Tricks
Many WordPress users know the wp-config.php file as the key to the WordPress database. It is where you set the database name, username, password, and location (among other things like security keys, database prefix, and localized language).
Here’s a screenshot of wp-config.php (aka the WordPress configuration file) for those who may not yet be familiar: